In offices, homes, schools, banks, and hospitals alike, our personal and professional lives leave a digital footprint. The vast connectivity that fuels modern convenience also introduces a range of risks many don’t fully appreciate until something goes wrong. Malicious code, data leaks, ransomware, and identity theft have evolved into daily realities for organisations and individuals who use the internet.
Building a strong cybersecurity posture is no longer just the domain of government agencies or tech giants.
Small businesses, schools, and even families must now take responsibility for their digital assets. The stakes have never been higher.
The Risk Landscape: What Are We Defending Against?
Every device that connects to the internet is potentially a target. Smartphones, laptops, routers—even smart fridges—represent points where sensitive information can be stolen or misused.
Attackers use tactics that range from crude phishing emails to sophisticated supply chain attacks that exploit trust between organisations.
Common Cyber Threats
- Phishing and Social Engineering: Deceptive tactics designed to trick users into revealing passwords or other confidential information.
- Malware: Harmful software, such as viruses, ransomware, or spyware, that disrupt operations or steal data.
- Denial-of-Service (DoS) Attacks: Flooding a system to overwhelm and disable it.
- Zero-Day Exploits: Attacks that exploit newly discovered vulnerabilities before patches are in place.
- Insider Threats: Current or former employees who intentionally (or accidentally) compromise security from within.
No matter the size of your business or the nature of your digital life, these risks are persistent and adapting all the time.
Why Cybersecurity Matters Now More Than Ever
More people use digital services every day, and the line between our physical and digital lives has blurred. Sensitive personal data, financial records, intellectual property, and even government secrets all move through digital channels.
Compromising any one of these can spell financial, reputational, or legal trouble.
Take the example of a hospital hit by ransomware: patient care is disrupted, confidential health records are exposed, and the fallout may last for years.
For businesses, the loss of intellectual property or client data can result in lawsuits and permanent reputation damage.
Even individuals can suffer severely, from drained bank accounts to ruined credit and privacy invasions.
Regulation is tightening too. In Australia, the Notifiable Data Breaches Scheme requires organisations to report significant leaks of personal information. Clients and suppliers increasingly demand proof of strong cybersecurity practices. Compliance has become essential to securing contracts and maintaining trust.
Building Strong Cyber Foundations
Everyone responsible for IT, no matter the sector or skill level, can put solid building blocks in place. The aim is to limit the chances of attack and recover quickly if things go wrong.
Some widely accepted strategies include:
1. Security by Design
This isn’t just about installing antivirus software. It’s about thinking proactively: planning protection into every system and process from the ground up.
Examples include default strong password requirements, account lockouts after several failed attempts, and ensuring software updates happen automatically wherever possible.
2. Human Firewalls: Training and Awareness
People are the first and last line of defence. Regular training helps individuals recognise phishing emails, avoid dangerous links, and report suspicious activity.
It only takes one well-meaning but distracted staff member to click something they shouldn’t, potentially impacting the whole organisation.
3. Layered Defences
Cybersecurity professionals refer to “defence in depth”: using layers of protection. Rather than relying on one tool or method, combine several strategies for broader coverage:
- Firewalls to block unauthorised access.
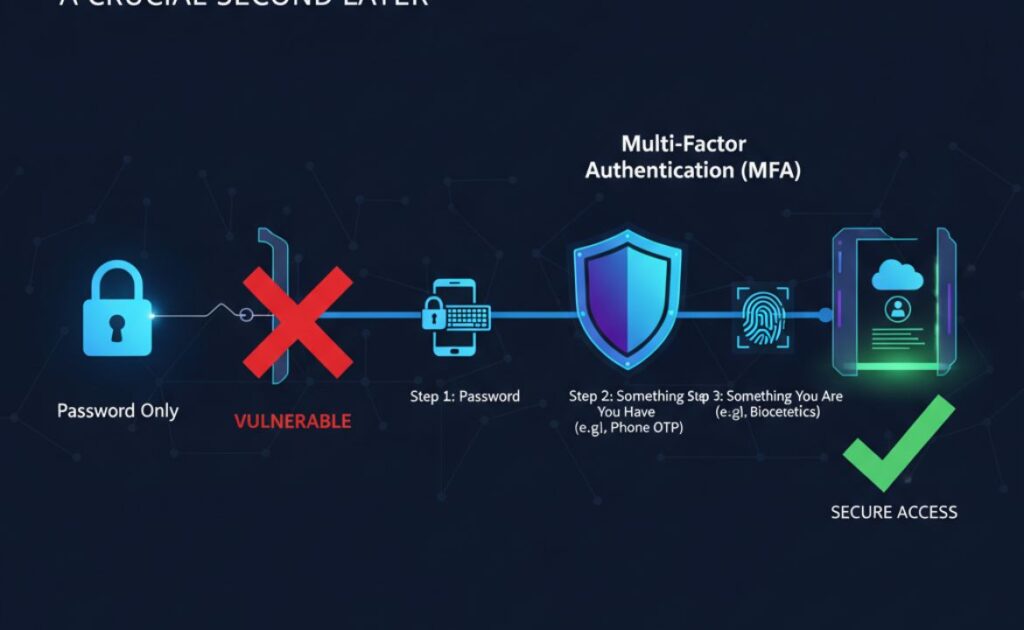
- Multi-factor authentication (MFA) to require more than just a password.
- Encryption to render stolen data unusable.
- Regular backups to ensure information can be restored after a breach.
4. Patch Management
Outdated software is one of the biggest entry points for attackers. Keeping all programs and systems up to date, with patches applied quickly, drastically reduces vulnerability. Automating this process wherever possible reduces human error.
5. Incident Response Planning
Having a clear action plan for when something goes wrong is just as important as preventing attacks. An incident response strategy should detail who does what, how customers are notified, how to get systems back online, and how to contain and assess the damage.
Top Threats and Their Common Defences
Threat Type
Common Defence
Phishing
Staff training, email filtering, MFA
Malware
Antivirus, patch management, restricted downloads
Ransomware
Frequent backups, user education, offsite storage
Data Breaches
Encryption, access controls, timely patching
Insider Threats
Role-based access, monitoring, regular audits
The Human Element in Cybersecurity
Technology forms the core, but people shape the perimeter. Even with the best systems, simple behaviours often decide success or failure.
Using strong, unique passwords across different online accounts.
Never letting devices out of sight in public areas.
Hesitating for a second before clicking an unexpected link.
Each habit forms a small but vital piece of the security puzzle.
Security fatigue is real: endless password changes, warnings, and complexity can drive people to take shortcuts. This is where leadership and culture matter. Cyber awareness must become a shared value, not just an IT problem.
Some organisations do this through engaging training, simulations, or incentives for spotting phishing attempts.
The Role of Cybersecurity Standards and Certifications
Credibility matters, particularly when other organisations or individuals are trusting you with their private information.
Australian government and international standards, like ISO 27001 or the Australian Cyber Security Centre’s Essential Eight, set benchmarks to aim for.
For businesses in finance, healthcare, law, or supply chain industries, professional certifications can give partners and clients reassurance. Engaging services that demonstrate compliance with these standards is increasingly a must-have rather than an optional extra.
Those seeking assistance with compliance and digital transparency initiatives should check platforms like LEI Service Australia, supporting businesses to meet regulatory expectations and build trust with their customers.
The Increasing Sophistication of Threats
Attackers aren’t standing still. Today’s criminals use artificial intelligence, automation, and social manipulation. They craft emails tailored to individuals, taking information from social media or previous breaches to make a scam look legitimate.
Even deepfakes are emerging to fool facial recognition or impersonate voices.
Traditional tools alone cannot keep pace. Security now involves machine learning to detect unusual patterns, proactive threat hunting, and information sharing across industries.
Small businesses may benefit from managed services or partnerships with security professionals who keep up with the ever-changing tactics.
Practical Steps Everyone Can Take
It may seem like digital defenders need endless resources, but some fundamental steps offer substantial protection:
- Set up MFA on all important accounts, from email to banking.
- Use a password manager to generate and store long, unique passwords.
- Schedule security updates for software and devices so nothing is left exposed.
- Make regular, encrypted backups of important data and test that they can be restored.
- Never share sensitive information by email or over the phone unless identity is confirmed beyond doubt.
When evaluating software, web platforms, or digital suppliers, ask about their security credentials and certifications. A trusted vendor will have nothing to hide.
The Broader Impact: Beyond the Organisation
Cybersecurity has effects that ripple outwards. When a small business secures its network, it protects its customers, its suppliers, and the community.
When a school teaches students how to protect their information, it creates privacy-aware adults for the future.
As governments put stringent requirements on critical infrastructure, the safety of all citizens benefits.
Security and privacy concerns are no longer confined to the IT department. Management, customer service, legal, finance, and even marketing must be brought into the conversation.
Informed staff who understand what is at stake can support efforts to protect data and avoid breaches.
Looking Ahead
Every year brings fresh threats and new opportunities in cybersecurity. Defensive strategies continue to develop, but so do the methods of those seeking to do harm.
Keeping informed, investing in technologies that offer real protection, and instilling a culture where security is everyone’s concern will continue to make all the difference.
The road ahead is challenging, but not insurmountable for those willing to act.